HEXA Staking - Smart Contract Audit Report
Summary
 HEXA is building a new staking platform that allows users to deposit ETH and earn rewards in HEXA tokens.
HEXA is building a new staking platform that allows users to deposit ETH and earn rewards in HEXA tokens.
Notes on the Contract:
- The HEXAStaking contract is used to facilitate multiple staking rounds in which users can deposit ETH into the contract and receive rewards in HEXA tokens in return.
- The owner must initialize the contract in order to allow deposits and withdrawals.
- Users can only deposit one time in an active staking round.
- Each round is broken down into a set of periods that can have differing rewards rates.
- On withdrawals, unpaid rewards are transferred from the HEXA Allowance address to the user.
- The project team must ensure the HEXA Allowance address has enough HEXA tokens to support the reward distributions, and that the proper approvals are in place to allow the HEXA tokens to be transferred.
- The HEXA token contract was not included in the scope of this audit, so we are unable to provide an assessment of this contract with regards to security.
- Rewards are calculated based on the time staked, the reward rate in the latest qualifying period, and the ETH to HEXA ratio set by the team; Users will not qualify for any rewards at all if withdrawing before the first period begins.
- Users can withdraw their funds staked in previous rounds at any time. Rewards for previous rounds do not accrue after the round has finished.
- The owner can start a new round at any time, as long as there is not a round currently running.
- The owner can end an ongoing round at any time.
- The owner can only set the reward rates and the periods for the next round only, as long as there is not a round currently running.
- The owner can set the ETH to HEXA ratio for reward distributions to any value, as long as there is not a round currently running.
- The team has worked with us to optimize this contract for gas efficiency.
- As the contract is implemented with Solidity v0.8.x, it is protected from overflows.
- The contract utilizes ReentrancyGuard to prevent re-entrancy attacks in applicable functions.
Audit Findings SummaryResolved Issues
- No security threats from outside attackers were identified.
- Ensure trust in the team prior to investing as they have substantial control in the ecosystem.
- Date: November 7th, 2021
- Updated: November 8th, 2021 to address an issue with withdrawing.
- The team addressed an issue within the contract that allowed users to withdraw more staked funds and rewards than were due.
External Threat Results
| Vulnerability Category | Notes | Result |
|---|---|---|
| Arbitrary Storage Write | N/A | PASS |
| Arbitrary Jump | N/A | PASS |
| Delegate Call to Untrusted Contract | N/A | PASS |
| Dependence on Predictable Variables | N/A | PASS |
| Deprecated Opcodes | N/A | PASS |
| Ether Thief | N/A | PASS |
| Exceptions | N/A | PASS |
| External Calls | N/A | PASS |
| Integer Over/Underflow | N/A | PASS |
| Multiple Sends | N/A | PASS |
| Suicide | N/A | PASS |
| State Change External Calls | N/A | Pass |
| Unchecked Retval | N/A | PASS |
| User Supplied Assertion | N/A | PASS |
| Critical Solidity Compiler | N/A | PASS |
| Overall Contract Safety | PASS |
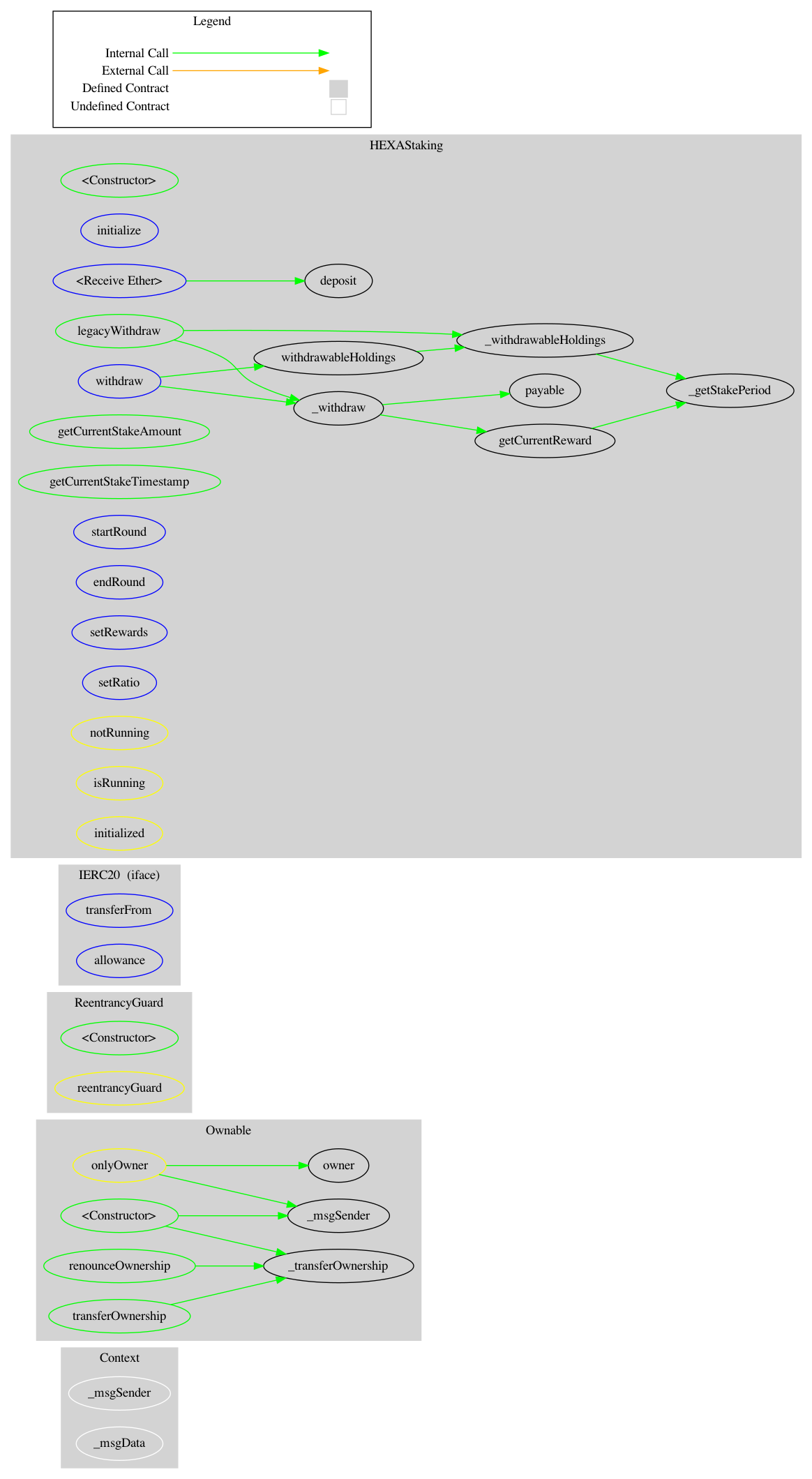
HEXAStaking Contract
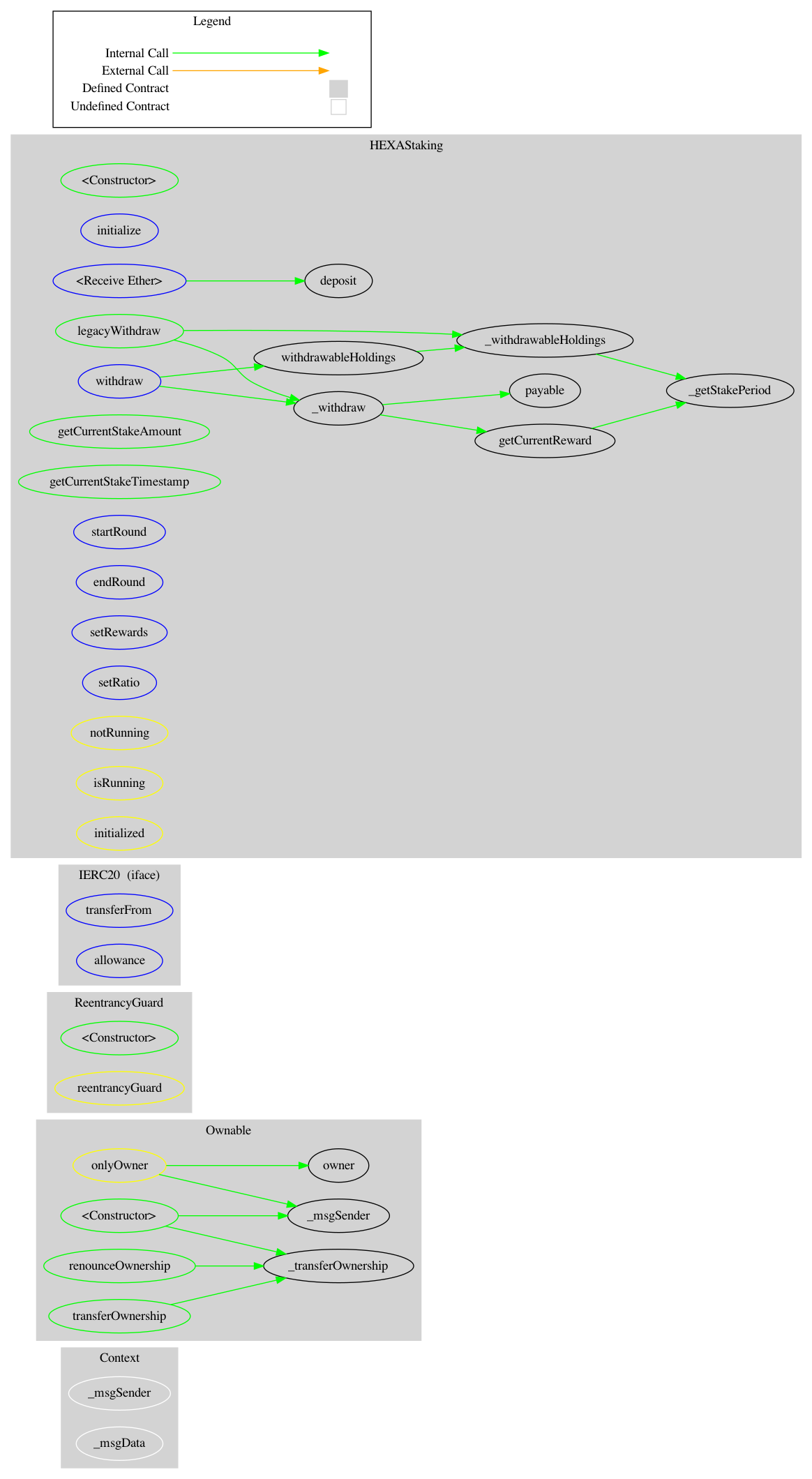
($) = payable function
# = non-constant function
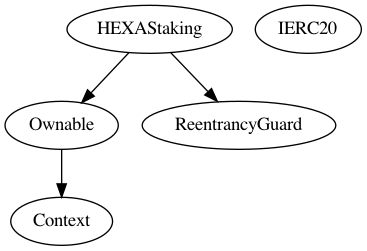
+ Context
- [Int] _msgSender
- [Int] _msgData
+ Ownable (Context)
- [Pub] #
- [Pub] owner
- [Pub] renounceOwnership #
- modifiers: onlyOwner
- [Pub] transferOwnership #
- modifiers: onlyOwner
- [Int] _transferOwnership #
+ ReentrancyGuard
- [Pub] #
+ [Int] IERC20
- [Ext] transferFrom #
- [Ext] allowance #
+ HEXAStaking (ReentrancyGuard, Ownable)
- [Pub] #
- [Ext] initialize #
- modifiers: onlyOwner
- [Pub] deposit ($)
- modifiers: initialized,isRunning,reentrancyGuard
- [Ext] ($)
- [Ext] withdraw #
- modifiers: initialized,isRunning,reentrancyGuard
- [Int] _withdraw #
- [Int] getCurrentReward
- [Pub] withdrawableHoldings
- [Pub] legacyWithdraw #
- modifiers: reentrancyGuard
- [Int] _withdrawableHoldings
- [Int] _getStakePeriod
- [Pub] getCurrentStakeAmount
- [Pub] getCurrentStakeTimestamp
- [Ext] startRound #
- modifiers: onlyOwner,notRunning
- [Ext] endRound #
- modifiers: onlyOwner,isRunning
- [Ext] setRewards #
- modifiers: onlyOwner,notRunning
- [Ext] setRatio #
- modifiers: onlyOwner,notRunning 